Posts by tag
book review
528 posts
The Art of Attention: Jill Christman’s If This Were Fiction: A Love Story in Essays
“If you really want to look at someone, then your only option is to look at yourself, squarely and deeply.”
Indiana Anomie: Budi Darma’s People from Bloomington
a portrait of the American tendency to keep the suffering of others at arm’s length as if misfortune were contagious, or to ruthlessly eliminate it entirely
From the Archive: Propelled by Questions: Animal by Dorothea Lasky
The animal spirit of poetry brings us closer to our own humanity.
From the Archive: Sketch Book Reviews: How I Became a Tree by Sumana Roy
An illustrated review of Sumana Roy’s new essay collection, HOW I BECAME A TREE!
A Breathtaking and Terrifying Expanse: Quan Barry’s When I’m Gone, Look for Me in the East
“The distances are staggering. It could take you an hour to drive to a spot on the edge of the horizon, yet that spot feels like it’s just within reach,” Barry writes. “This is what it means to live on the steppe. There are no walls between you and nature. You are nature.”
From the Archive: Sketch Book Reviews: Girlhood by Melissa Febos
An illustrated review of Melissa Febos’s new essay collection, GIRLHOOD!
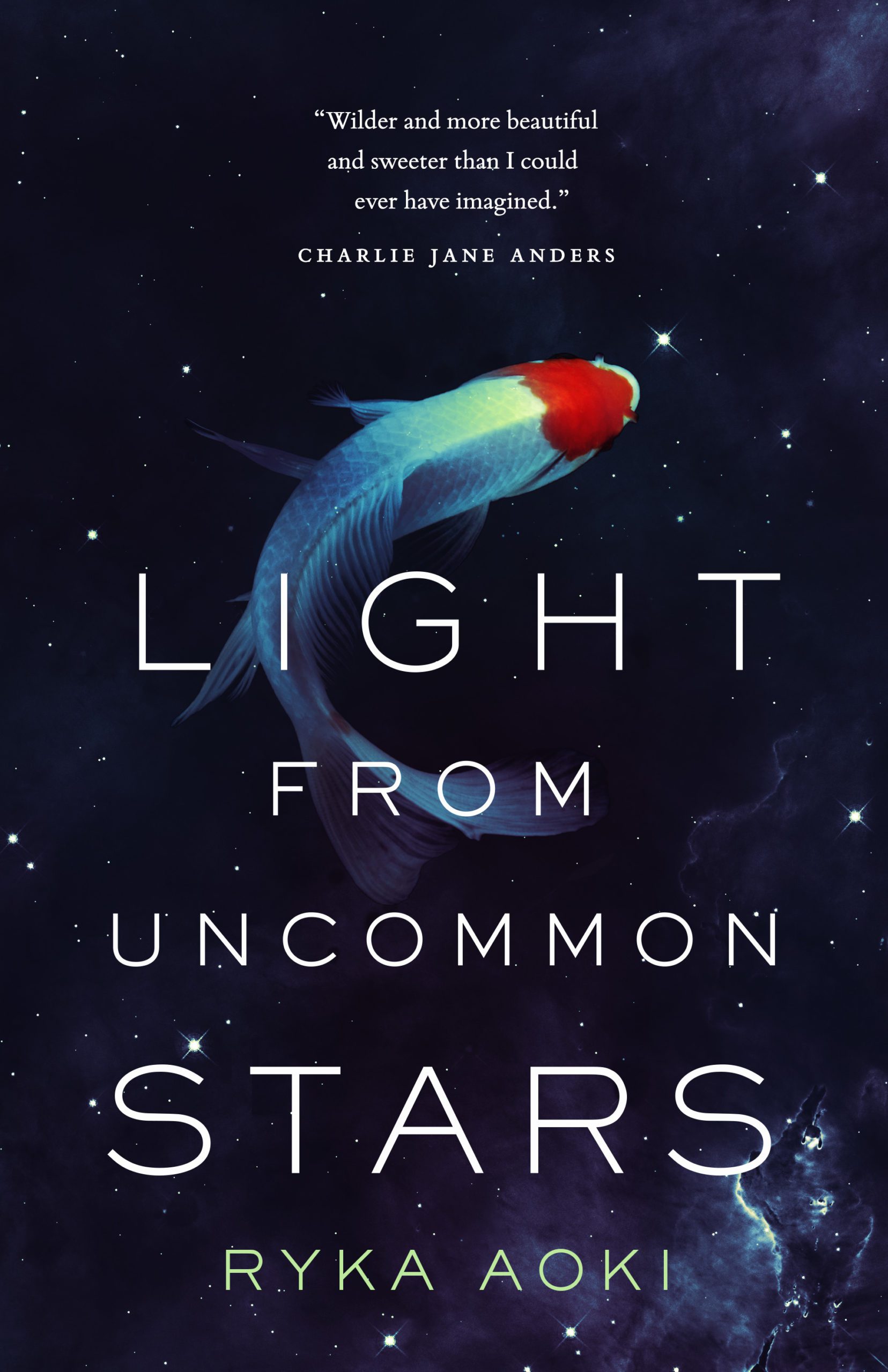
Defying Gravity: Ryka Aoki’s Light from Uncommon Stars
This book is disarmingly—in fact, unnervingly—amoral.
Still, Life: Intimacies by Katie Kitamura
I’ll never see Kitamura’s exhibition in real life, but I’m still grateful to have been invited to the opening.
How to Watch While Being Watched: Aisha Sabatini Sloan’s Borealis
The experience, rather than linear, is borealian.
Down the Rabbit Hole: Eugene Lim’s Search History
Lim has written before about experimental fiction and the need to slough off such conventions of narrative as plot.
Metaphor by Any Means Necessary: Destiny O. Birdsong’s Negotiations
Metaphor can make life more bearable, meaningful, or simply comprehensible.